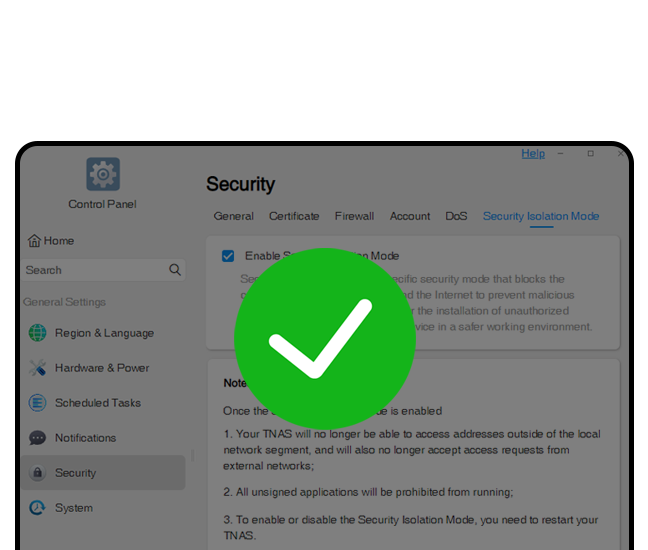
/ Security Isolation Mode

Kernel security level
Using a digital signature based on kernel level, once the security isolation mode is enabled, any programs that are not signed by the system will be blocked from running, effectively halting viruses or malicious code.Self-isolation
The Security Isolation Mode can effectively prevent illegal in-stack and out-stack access to the external network by establishing an isolation barrier that only allows legal access within the local network, protecting the system from external malicious attacks.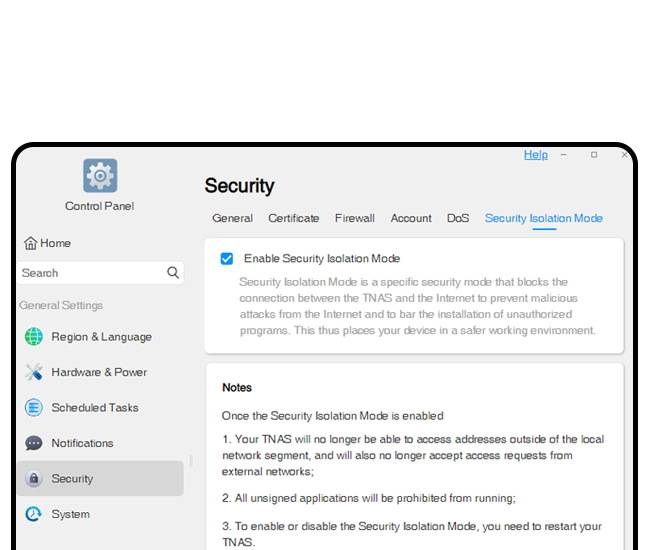
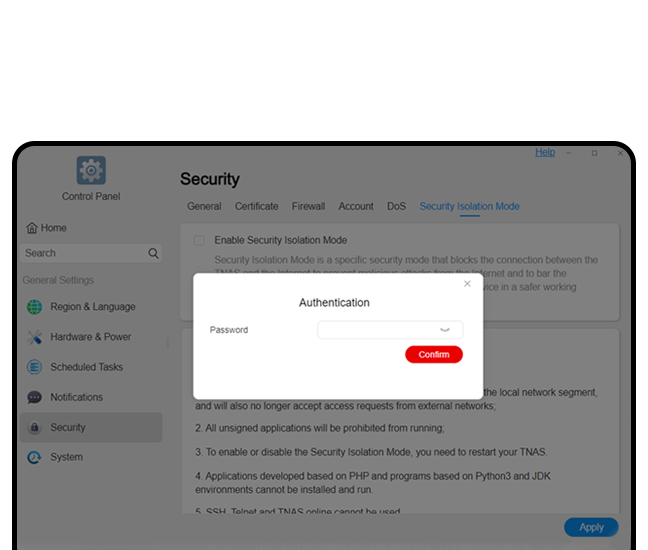
Secondary advanced protection
In order to prevent any security barriers and system protection measures from attacks and tampering, the Security Isolation Mode offers secondary password verification protection. Deleting or modifying all configuration information related to security protection measures thus requires additional password verification, effectively preventing hackers from damaging defenses.Strong blocking
Any code based on Java, php, or Python is blocked from execution, effectively preventing the system from being injected with malicious code that might threaten data security.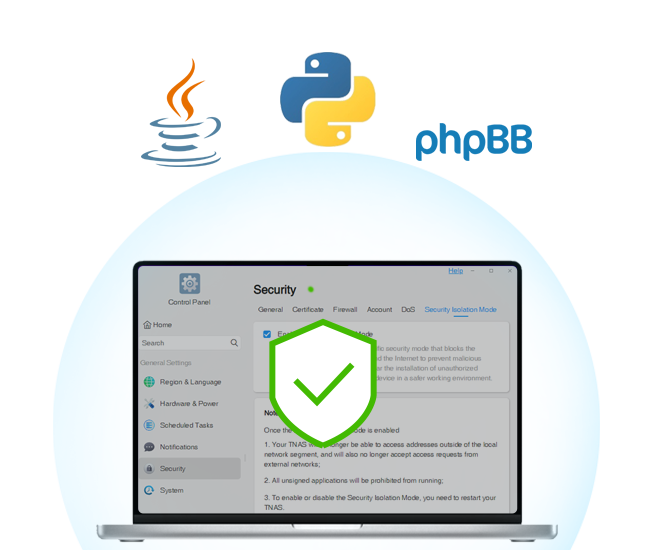

Applicable cases
. Enterprises or organizations that are extremely sensitive to data security;. External network services that must be closed and isolated, and which do not need to access an external network or provide remote access;
. Systems that only use TNAS to provide file storage, and which have no need to run web pages, databases, mail services, virtual machines, or other remote applications;
. Applicable industries include the military, the judicial system, power companies, scientific research, and medicine.


